In 2024, the Change Healthcare breach exposed over 100 million patient records and disrupted claims processing across the entire United States. It was the largest healthcare data breach in history, and it cost UnitedHealth Group an estimated $2.45 billion in response and recovery.
Healthcare data security protects sensitive patient information. This includes Protected Health Information (PHI), electronic PHI (ePHI), and Personally Identifiable Information (PII). The goal is to prevent unauthorized access, theft, and misuse across all systems that handle patient information.
This guide covers everything you need to know about protecting healthcare data: the current threat landscape, global compliance requirements (not just HIPAA), proven best practices, application-specific security guidance, enterprise architecture considerations, and realistic cost expectations.
Key Takeaways
- Healthcare data security protects PHI, ePHI, and PII from unauthorized access, breaches, and misuse
- HIPAA compliance is the baseline, not the ceiling, of healthcare data protection
- Ransomware and third-party vendor attacks remain the top two threats in 2026
- A zero-trust security model combined with encryption and access controls forms the core defense
- Building security into custom software from day one (DevSecOps) is more effective and cheaper than retrofitting
What Is Healthcare Data Security?
Healthcare data security covers the strategies, technologies, and processes that protect digital healthcare information from unauthorized access, corruption, and breaches. It applies to data at rest, in transit, and in use across hospitals, clinics, health tech platforms, insurance providers, and their partners.
Why is healthcare a top target? The data itself. A stolen credit card sells for $1 to $2 on the dark web. A complete healthcare record sells for $250 to $1,000. It contains Social Security numbers, medical histories, insurance details, and billing information. Unlike a credit card, you can’t cancel or reissue a medical history.
Types of Healthcare Data That Need Protection
| Data Type | What It Includes | Example |
| PHI (Protected Health Information) | Any health information linked to an individual | Medical diagnoses, treatment records, lab results |
| ePHI (Electronic PHI) | PHI created, stored, or transmitted electronically | EHR records, digital prescriptions, patient portal data |
| PII (Personally Identifiable Information) | Data that identifies a person | Name, SSN, date of birth, address |
| Financial/Billing Data | Payment and insurance information | Insurance ID, billing codes, credit card numbers |
Every system that stores, processes, or transmits any of these data types falls under information security requirements.
Why Healthcare Data Security Matters More Than Ever?
Three numbers tell the story:
- $10.93 million: average healthcare breach cost (IBM Cost of a Data Breach Report). Highest of any industry for 13 straight years.
- 54% of patients would consider switching providers after a breach (Ponemon Institute, 2023).
- 100+ million records exposed in the Change Healthcare breach alone.
For healthcare organizations, information security isn’t a compliance checkbox. It’s a business survival issue
The attack surface keeps expanding. Four trends are driving this:
- Telehealth visits increased 38x during the pandemic and remain elevated
- Connected medical devices are projected to reach 50 billion by 2028
- Cloud adoption in healthcare is accelerating rapidly
- AI integration in clinical workflows creates new vulnerability categories eeps expanding. Four trends are driving this:
Top Healthcare Data Security Threats and Challenges
Healthcare cybersecurity faces a threat landscape that is both broad and deeply specific to the industry. Here are the most critical healthcare cybersecurity challenges in 2026:
| Threat | Why it matters | Impact | Example |
| Ransomware | Disrupts operations and threatens patient safety, increasing pressure to pay | System downtime, delayed care, financial loss | 67% of healthcare orgs hit in 2024; avg downtime ~18.7 days |
| Third-party vendors | Data shared across multiple partners creates external entry points | Supply chain breaches, large-scale exposure | Change Healthcare breach via compromised vendor credentials |
| Insider threats | High staff turnover and broad access increase risk of misuse | Unauthorized disclosure, access violation | ~35% of breaches linked to internal users |
| Legacy systems | Outdated systems lack patches and modern security controls | Vulnerabilities exploited by attackers | Systems 15–20 years old still in use |
| IoT medical devices | Devices often run outdated firmware and are hard to patch | Expanded attack surface, device-level breaches | Infusion pumps, monitors with limited security updates |
| AI-powered attacks | Phishing, deepfakes, automated scanning | Credential theft, unauthorized access, large-scale data breaches | AI-generated emails mimic hospital admins with near-perfect accuracy |
AI threats deserve special attention.
Attackers now use generative AI to create phishing emails that closely mimic internal communication, making them difficult for clinical staff to detect. Deepfake technology can also bypass voice-based patient authentication systems. At the same time, automated tools can scan networks for vulnerabilities far faster than any manual process.
To keep up, organizations need AI-powered security capabilities. This requires not just tools, but experienced teams who understand how to build and deploy AI for real-world threat detection.
Global Healthcare Data Security Regulations
Most guides on this topic focus exclusively on HIPAA. That’s not enough. If your organization operates across borders or serves international patients, you need a global compliance view.
Global Compliance Comparison Table
| Aspect | HIPAA (US) | GDPR (EU/UK) | PDPA (Singapore) | Privacy Act (Australia) | CCPA/CPRA (California) |
| Scope | Healthcare entities and business associates | Any organization processing data of EU/UK residents (including non-EU entities) | Organizations collecting personal data of Singapore residents | Most organizations >$3M AUD and all healthcare providers | Businesses meeting revenue, data volume, or processing thresholds |
| Data covered | PHI (including ePHI) | All personal data | Personal data | Personal information | Personal information |
| Consent model | Implied for treatment; required for other uses | Explicit opt-in | Consent required, with limited exceptions | Generally required, with exceptions | Opt-out for data sale/sharing |
| Breach notification | Within 60 days to HHS | Within 72 hours to supervisory authority | As soon as practicable to PDPC | As soon as practicable to OAIC | Required under California breach notification laws |
| Max penalty | ~$1.5M–$2M per violation category per year | Up to €20M or 4% of global annual revenu | Up to 10% of annual turnover (capped at SGD 1M previously) | Up to AUD $50M, 3× benefit, or 30% of adjusted turnover (whichever is higher) | Up to $7,500 per intentional violation |
| Key requirement | Administrative, physical, and technical safeguards (Security Rule) | DPIA, DPO appointment, strong data subject rights | DPO appointment, consent management, accountability | Australian Privacy Principles (APPs), breach notification | Consumer rights (access, delete, opt-out), privacy disclosures |
Multi-Jurisdiction Strategy
Don’t build separate compliance programs for each country. Start with the strictest standard (typically GDPR), then layer local requirements like HIPAA or PDPA on top. Frameworks like NIST and HITRUST help unify this approach. Custom software can enforce different rules per region without separate systems.
Security vs. Compliance
Compliance = legal minimum.
Security = real protection.
The Change Healthcare system was HIPAA-compliant but lacked MFA. Compliant, not secure.
This gap is critical in software. AI can generate code fast, but it doesn’t guarantee security. Systems still need experienced architects to ensure proper controls like encryption, logging, and secure APIs.
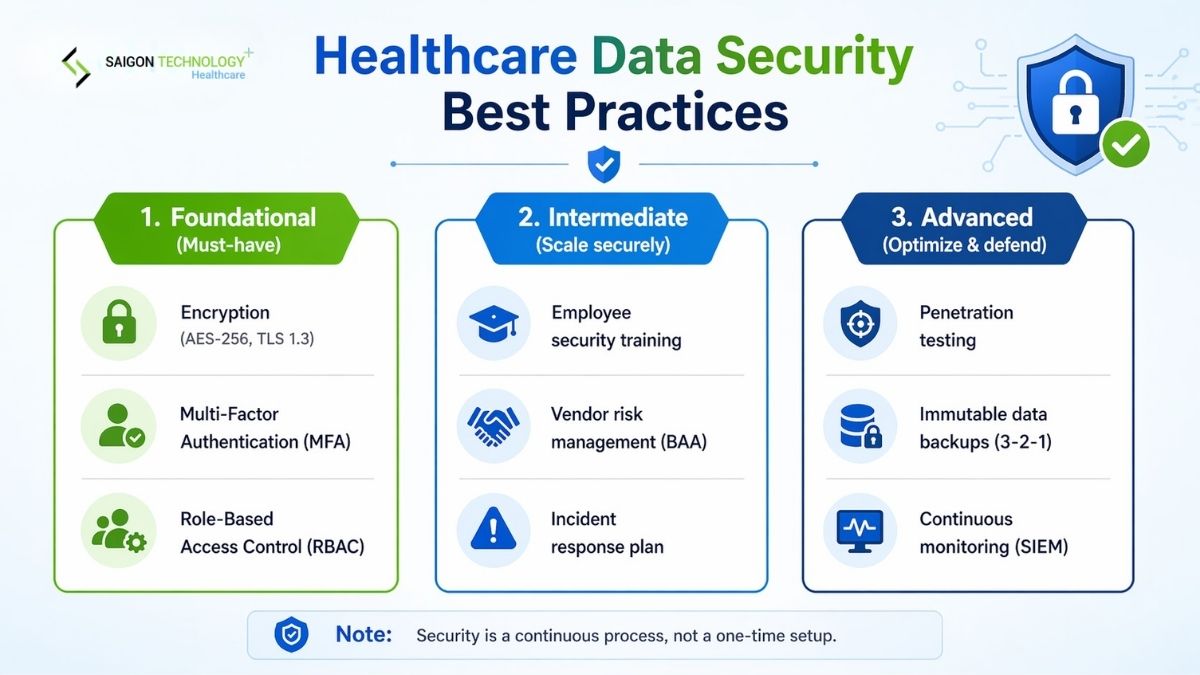
Healthcare Data Security Best Practices
Here are proven healthcare security solutions, organized from foundational to advanced.
Foundational (implement first):
- Encryption everywhere. AES-256 for data at rest, TLS 1.3 for data in transit. This is non-negotiable. Encrypted data is useless to attackers even if they breach your perimeter.
- Multi-factor authentication (MFA). Require MFA for all systems that access patient data. This single control would have prevented the Change Healthcare breach.
- Role-based access control (RBAC). Apply the principle of least privilege. A billing clerk should not have access to clinical notes, and a nurse should not have access to financial systems.
Intermediate (build on the foundation):
- Employee security training. Run quarterly phishing simulations and security awareness programs. Track completion and click rates. Target clinical staff specifically.
- Vendor risk management. Require Business Associate Agreements (BAAs) for all vendors handling PHI. Conduct annual security assessments. Monitor vendor access logs continuously.
- Incident response planning. Document, test, and update your incident response plan at least annually. Run tabletop exercises with your leadership team.
Advanced (strengthen your posture):
- Regular penetration testing. Conduct both internal and external penetration tests at least annually. Test your web applications, APIs, and network infrastructure.
- Data backup with immutability. Follow the 3-2-1 backup rule: 3 copies, 2 different media, 1 offsite. Use immutable backups that attackers cannot encrypt or delete.
- Continuous monitoring and SIEM. Deploy security information and event management tools to detect anomalies in real time. CISA’s healthcare cybersecurity resources provide additional guidance on monitoring frameworks.
Building a Zero-Trust Security Model for Healthcare
Traditional perimeter-based security assumes everything inside the network is trusted. Zero-trust assumes nothing is trusted, ever. Every access request must be verified regardless of where it originates.
For healthcare, zero-trust implementation follows four phases:
- Identity. Implement strong IAM with MFA and single sign-on (SSO) across all clinical and administrative systems.
- Network. Apply microsegmentation to isolate clinical systems, medical devices, guest Wi-Fi, and administrative networks from each other.
- Workload. Secure containerized applications and microservices with runtime protection and vulnerability scanning.
- Data. Classify all data by sensitivity level. Apply encryption and access policies based on classification.
Healthcare Data Security for Key Applications
Security requirements differ by application. Here’s what matters for the four highest-risk categories.
Patient Portals
Patient portals are your most exposed external attack surface. If one patient can view another’s records, you have a breach.
- Mandatory MFA for all patient logins
- Secure session management with auto-timeouts
- API security for all data retrieval endpoints
- Complete HIPAA audit logging for every data access
- Watch for: broken authentication and insecure direct object references
Telehealth Platforms
Telehealth platforms handle live video, audio, and stored recordings. All of it is ePHI.
- End-to-end encryption for all video and audio streams
- Stored recordings need the same encryption as any ePHI
- Cross-border sessions flow across jurisdictions with different data privacy laws
- You need configurable compliance controls per region
EHR/EMR Systems
EHR systems hold the most comprehensive patient data. That makes them the highest-value target and the hardest to secure.
- Granular access controls with complete audit trails
- Database encryption + secure HL7 FHIR API endpoints
- Tested backup and disaster recovery procedures
- Every integration point (labs, pharmacies, billing) is a potential vulnerability
Remote Patient Monitoring and IoT Medical Devices
RPM and IoT devices transmit data continuously over wireless, often with firmware that was never designed with security in mind.
- Device authentication before network access
- Data encryption in transit at all times
- Firmware update security and validation
- Network segmentation to isolate IoT from core clinical systems
Modern remote patient monitoring platforms with AI-powered features detect anomalies in both patient data and system access. The FDA’s cybersecurity guidance should inform procurement decisions.
Healthcare Data Security Architecture: Enterprise View
Here’s how patient information flows through a healthcare system and where controls apply.
Data Flow and Security Layers
Patient information passes through six distinct security layers:
| Layer | Security Controls | Threat Mitigated |
| User Device | Device management, endpoint protection | Compromised devices |
| Authentication | MFA, SSO, biometrics | Credential theft |
| Frontend/WAF | Web application firewall, input validation | Injection attacks, XSS |
| API Gateway | Rate limiting, token validation, API security | API abuse, unauthorized access |
| Business Logic | RBAC, audit logging, data masking | Privilege escalation, insider threats |
| Database | AES-256 encryption at rest, access controls | Data exfiltration |
| Backup | Immutable backups, offsite disaster recovery | Ransomware, data loss |
Each layer enforces controls independently. One compromised layer doesn’t expose the rest. That’s defense in depth.
Cloud vs. On-Premise: Security Architecture Trade-offs
Where your system runs also affects how security is handled.
In cloud computing in healthcare (AWS, Azure, GCP), security is shared. The provider protects the infrastructure, but your organization is still responsible for securing records, user access, and applications.
You also need to consider storage location. Some regulations, like GDPR, require patient records to be stored in specific regions.
On-premise systems give you full control, but your team must handle everything, from infrastructure to security operations.
Because of this, many healthcare organizations use a hybrid approach. Sensitive data stays on-premise, while applications run in the cloud for better scalability.
How Much Does Healthcare Data Security Cost?
Healthcare data security is not a single line item. It spans technology, people, processes, and compliance across the entire organization.
Cost Breakdown by Organization Size
| Category | Small Practice (<50 staff) | Mid-size Hospital (50-500) | Enterprise Health System (500+) |
| Security infrastructure | $15,000 – $50,000/yr | $100,000 – $500,000/yr | $1M – $5M+/yr |
| Compliance & audit | $5,000 – $25,000/yr | $50,000 – $200,000/yr | $200,000 – $1M+/yr |
| Employee training | $2,000 – $10,000/yr | $15,000 – $50,000/yr | $50,000 – $250,000/yr |
| Incident response retainer | $5,000 – $15,000/yr | $25,000 – $100,000/yr | $100,000 – $500,000/yr |
| Custom security software | Project-based ($25K-$100K) | $100,000 – $500,000 | $500,000 – $2M+ |
Sources: Ponemon Institute, HIMSS, Gartner healthcare security benchmarks. Ranges are estimates and vary by region, vendor, and organizational maturity.
Key Cost Drivers
Six factors determine where your organization falls within these ranges:
- Number of endpoints and connected devices
- Data volume and sensitivity classification
- Number of jurisdictions and compliance frameworks
- Legacy system remediation needs
- Custom vs. off-the-shelf security tooling
- Whether security is managed in-house or outsourced.
The ROI of Proactive Security Investment
A mid-size hospital spending $300,000 per year on security invests about 3% of the average breach cost ($10.93 million). This also reduces cyber insurance premiums by 15–30% and speeds up regulatory approvals.
Building security into custom healthcare software from day one costs 30–50% less than retrofitting later, a trend consistently validated by NIST’s SDLC research.
The Role of Custom Software in Healthcare Data Security
Off-the-shelf software relies on standardized configurations, which often leads to generic and predictable security.
Custom-built software embeds security from day one. With a DevSecOps approach, continuous security testing and validation are built into every stage of the development pipeline.
What you get:
- Access controls aligned with your exact roles, not generic templates.
- Encryption designed for your specific data flows.
- Compliance modules configurable per jurisdiction.
- Audit logging built for your reporting requirements.
A dedicated team with healthcare expertise ensures systems are both secure and usable. Even MVPs should include core security controls, especially in sensitive areas like mental health applications.
The biggest mistake teams make is treating security as a phase. It’s not something you add. It’s something you build.
FAQs
What are the biggest threats to healthcare data security?
The five most critical threats include:
- Ransomware attacks that lock clinical systems and threaten patient safety
- Third-party vendor vulnerabilities and supply chain attacks
- Insider threats from employees with excessive access
- Legacy systems running unpatched software
- AI-powered attacks, including phishing and social engineering targeting clinical staff
What are the 5 main HIPAA rules?
The five HIPAA rules are:
- Privacy Rule: governs the use and disclosure of PHI
- Security Rule: requires administrative, physical, and technical safeguards for ePHI
- Enforcement Rule: defines investigation and penalty procedures
- Breach Notification Rule: requires notification to HHS, patients, and media
- Omnibus Rule: extends requirements to business associates and strengthens penalties
What is the difference between HIPAA and GDPR?
HIPAA applies only to healthcare entities and business associates in the US, focusing on PHI and ePHI.
GDPR applies to all organizations processing personal data of EU and UK residents across industries. It requires:
- Explicit user consent
- Broader individual rights such as data access and erasure
- Faster breach notification: 72 hours versus 60 days under HIPAA
GDPR penalties are also significantly higher, reaching up to €20M or 4% of global revenue.
What healthcare data privacy laws apply outside the US?
Key regulations include: GDPR (EU/UK) for all personal data processing, Singapore’s PDPA for organizations collecting personal data from Singapore residents, and Australia’s Privacy Act 1988 (with 2024 amendments) that impose Australian Privacy Principles and mandatory breach notification.
How much does healthcare data security cost?
Costs range from $27,000-$100,000/year for small practices to $1.85M-$7.75M+ for enterprise health systems, depending on organizational size, number of endpoints, compliance requirements, and security maturity. The critical context: a single breach costs $10.93M on average, making proactive security investment roughly 3-10% of what a breach would cost.
How can healthcare organizations prevent data breaches?
Seven essential prevention strategies:
(1) Enforce MFA across all systems
(2) Encrypt all data at rest and in transit
(3) Implement role-based access control with least privilege
(4) Conduct quarterly employee security training and phishing simulations
(5) Assess and monitor all third-party vendors
(6) Deploy continuous monitoring and SIEM tools
(7) Maintain and regularly test an incident response plan.
How is AI changing healthcare data security?
AI is transforming how attacks are carried out. Attackers use generative AI to create highly convincing phishing emails, produce deepfakes for identity fraud, and run automated vulnerability scanning at scale. These techniques make attacks faster, more realistic, and harder to detect.
At the same time, healthcare organizations use AI to strengthen defense. AI enables real-time threat detection, anomaly monitoring, and faster incident response. This dual use of AI makes healthcare security more dynamic and requires continuous adaptation.
Conclusion
Healthcare data security is not a one-time project. It is an ongoing discipline that spans technology, compliance, architecture, and culture. As threats evolve and regulations become more complex, organizations must treat security as a core business priority.
The most effective approach is clear: build security into systems from the start. Whether through zero-trust architecture, DevSecOps, or custom software, security by design is always more effective and less costly than fixing issues later.
At Saigon Technology, we apply this principle in every project, helping healthcare organizations build systems that are secure, compliant, and scalable from day one. If you are planning a healthcare software initiative, contact our team to design a security-first solution tailored to your requirements.