Healthcare data breaches hit record highs in 2024, exposing more than 275 million patient records according to HIPAA Journal. HIPAA penalties can range from $100 to $50,000 per violation, with annual penalties reaching millions of dollars for systemic compliance failures.
HIPAA compliant app development is the process of designing and building healthcare software that meets federal privacy and security requirements under HIPAA, protecting patient data across every layer of your application, from mobile front end to cloud infrastructure.
For healthcare organizations and digital health companies, building a HIPAA compliant app is no longer optional. Whether you’re developing a mobile application, a web platform, or a full-stack clinical tool, HIPAA compliant software development requires meeting strict privacy and security standards across every layer of your stack.
This guide covers requirements, key security safeguards, the development process, estimated 2026 costs, and common compliance mistakes. A downloadable HIPAA development checklist for pre-launch reviews is included at the end.
Key Takeaways
- HIPAA applies to any app that stores or processes Protected Health Information (PHI).
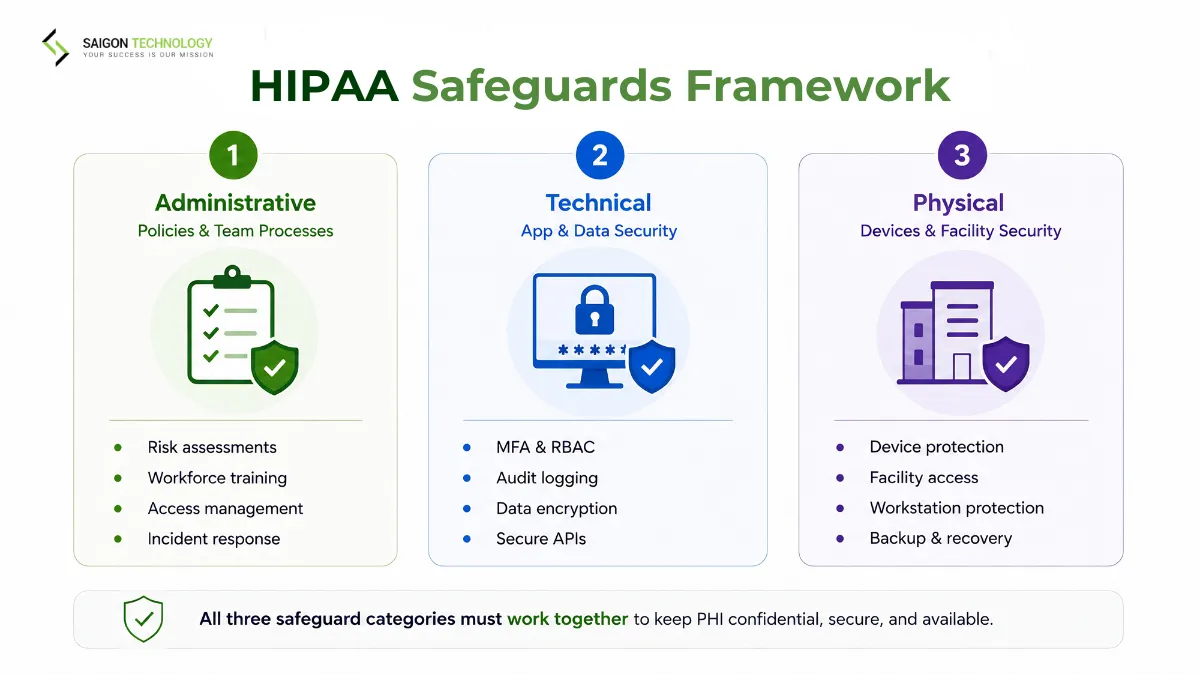
- Compliance requires three layers: Administrative, Physical, and Technical Safeguards.
- Critical technical requirements: encryption, audit logging, role-based access control, automatic logoff, and unique user identification.
- A signed Business Associate Agreement (BAA – a legal contract defining how PHI may be used and disclosed) is mandatory with every vendor that touches PHI.
- 2026 build cost: $50K to $300K+, depending on scope. Ongoing compliance runs $30K to $150K per year.
What Is HIPAA Compliant App Development?
HIPAA compliant app development is the process of building healthcare software that protects Protected Health Information (PHI) under the HIPAA Privacy Rule, Security Rule, and Breach Notification Rule.
An app may need HIPAA compliance if it handles PHI for a covered entity or business associate.
This commonly includes:
- Telehealth apps
- Patient portals
- EHR and EMR systems
- Remote patient monitoring (RPM) platforms
- Healthcare SaaS products
- mHealth apps
HIPAA compliance involves more than encryption alone. Healthcare applications must implement administrative safeguards, technical safeguards, and physical safeguards. These safeguards affect infrastructure, user access, data storage, audit logging, vendor management, and ongoing security operations.
Covered Entity vs Business Associate
| Type | Description | Common Examples |
| Covered Entity | Organizations directly regulated under HIPAA that provide healthcare services or manage health information | Hospitals, clinics, physicians, pharmacies, health insurers |
| Business Associate | Vendors or partners that process PHI on behalf of a covered entity | Development companies, cloud providers, analytics platforms, telehealth vendors |
What Counts as Protected Health Information (PHI)?
PHI includes both medical records and personally identifiable data connected to healthcare services.
Examples include:
- Diagnoses, prescriptions, and treatment plans
- Patient names, phone numbers, and email addresses
- Insurance information and account numbers
- IP addresses, device identifiers, and biometric data
- Patient photographs and facial recognition data
Consumer wellness applications may fall into a gray area. However, once an app connects to a healthcare provider, integrates with an EHR system, or processes PHI, HIPAA obligations may apply.
HIPAA Requirements for App Development
The HIPAA Security Rule organizes compliance into three safeguard categories. Your app must address all three.
Administrative Safeguards
The policies and procedures that protect PHI operationally. No code covers these. They are the compliance backbone.
| Requirement | What it involves |
| Risk Analysis | Document threats to PHI annually |
| Risk Assessment | Rate likelihood and impact per threat |
| Workforce Training | Annual HIPAA policy refreshes |
| Access Management | Define who can access what data, and when |
| Incident Response | Named owners, escalation paths, breach plan |
| BAA Management | Track every vendor contract with PHI access |
OCR enforcement data shows administrative gaps consistently drive the largest settlements. Teams that skip this layer because it is “not shippable code” pay for it later.
Technical Safeguards
The controls built into your application and infrastructure. Misconfigurations here cause the most breaches.
| Control | Requirement |
| Access Control | Unique user identification for every account |
| RBAC | Least-privilege access enforced by job function |
| Authentication | Multi-factor authentication for admin and clinical roles |
| Automatic Logoff | Enforced on inactivity, both web and mob |
| Encryption at Rest | AES-256 or stronger for all databases and storage |
| Encryption in Transit | TLS 1.2+ for all network communication |
| Audit Logging | Immutable logs capturing every read, write, and config change |
| Data Integrity | Mechanisms to detect unauthorized PHI modification |
Encryption requirements for mobile devices deserve special attention. Any PHI stored locally on a device, including cached data, must be encrypted at rest and protected by device-level controls.
Physical Safeguards
For cloud-native apps, hosting providers cover much of this. Your team still owns:
- Device controls for workstations and mobile devices accessing the app
- Data backup and disaster recovery with tested restore procedures
- Emergency access procedures for critical clinical scenarios
- Secure data storage policies across production and dev environments
Lost or stolen devices remain a common source of reportable healthcare breaches. Teams building mobile app development services should plan physical safeguard controls from the architecture phase, not as an afterthought.
Step-by-Step HIPAA Compliant Software Development Process
Building healthcare software under HIPAA requires a different process than standard software development. Whether you are building a mobile app, a web platform, or a backend API layer, compliance work happens alongside feature development, not after launch.
The seven-step framework below covers how teams plan, build, secure, and maintain compliant healthcare applications. This is the approach Saigon Technology uses for HIPAA compliant software development projects that handle PHI.
Step 1: HIPAA Risk Assessment and Scoping
Every project starts with a documented risk assessment. The team inventories PHI categories, maps data flows from collection through storage and transmission, and identifies threats at each stage. The output is a written Risk Assessment and a PHI data flow diagram. This document drives every architectural decision that follows.
Step 2: Architecture Design with HIPAA-Eligible Services
Infrastructure selection comes next. Sign a BAA before any production traffic touches the platform.
| Cloud Platform | Key HIPAA-Eligible Services |
| AWS | EC2, RDS, S3, CloudTrail, Lambda. Reference the official AWS HIPAA Eligible Services list before selecting any service. |
| Microsoft Azure | Azure Health Data Services, Azure Confidential Computing |
| Google Cloud | Google Cloud Healthcare API with native FHIR-compliant APIs |
Many teams use managed HIPAA hosting providers that bundle infrastructure, BAA, and operational controls. For most mid-sized healthcare applications, this can significantly reduce time-to-launch for many mid-sized healthcare applications.
Plan FHIR API support at this stage if your app will exchange data with EHR systems. Retrofitting later is significantly more expensive.
Step 3: Secure Development Lifecycle (SDLC)
A secure development lifecycle (SDLC) builds compliance into every commit. For teams pursuing software modernization of legacy healthcare systems or building custom software development solutions, this stage also covers migration risk and data integrity and interoperability requirements.
- Static and dynamic code analysis on every pull request
- Regular code reviews with a security-trained reviewer on sensitive paths
- Change control procedures for every production deployment
- Automated testing tools covering functional and security suites
- Pre-launch validation running compliance checks before every release
Step 4: Implementing Technical Controls
This is where most of the coding happens. The team builds user authentication, RBAC (Role-Based Access Control), encryption pipelines, audit log flows, and automatic logoff logic.
A common pattern: centralized policy engine for access decisions, immutable append-only logs shipped to AWS CloudTrail or equivalent, short-lived authentication tokens with refresh flows.
For healthcare platforms incorporating artificial intelligence and machine learning compliance requirements, this stage adds model access logging and PHI handling guardrails for AI pipelines. Apps using Internet of Things (IoT) and wearable device integration also need device-level data handling controls defined here.
Step 5: Vendor and BAA Management
Every vendor that touches PHI needs a signed BAA (Business Associate Agreement). The obvious ones include cloud providers and databases. Easy-to-miss ones:
- Push notification services
- Email and SMS gateways
- Error tracking platforms
- Analytics and session recording tools
- Customer support systems
The BAA must include HIPAA language around permitted uses and disclosures, breach notification obligations, and procedures for data modification and deletion when the relationship ends. Your vendor selection process should treat BAA readiness as a primary criterion, especially when working with a dedicated development team on a long engagement.
Recognized security practices, as referenced under the HITECH RFI framework, should also be documented at this stage as a mitigating factor in any future enforcement review.
Step 6: Testing and Pre-Launch Validation
- Penetration testing by an external security firm
- Vulnerability scans on every infrastructure component
- Compliance audit verifying every Security Rule requirement
- BAA verification for every vendor in the production stack
- Final checks on configuration, secrets management, and logging coverage
Common failures we find here: S3 buckets missing encryption, analytics SDKs transmitting device IDs alongside PHI, logging endpoints that strip PHI from app logs but not infrastructure logs.
Step 7: Launch and Ongoing Compliance Maintenance
Most guides stop at launch. This step is where sustained HIPAA compliance actually lives.
- Real-time anomaly detection for suspicious access patterns
- Ongoing audit log monitoring with documented review procedures
- Incident response protocols ready for HIPAA’s 60-day notification window
- Annual risk assessments updated as the application evolves
- Quarterly BAA reviews and renewals
- Workforce training refreshes for new staff
Skipping this step is the most common path to an OCR enforcement action. Build the program before you need it.
Need help scoping this process for your project? Review our healthcare software development services to see how we structure each engagement.
HIPAA Compliant App Development Cost
The realistic 2026 cost ranges below reflect what we see across active healthcare projects, broken into three tiers.
| Project Tier | Description | Typical Timeline | Build Cost | Annual Compliance Cost |
| MVP / Pilot | Single use case, mobile-only application with one integration | 3–5 months | $50K – $90K | $20K – $35K |
| Production | Web + mobile platform with EHR integration, RPM, or secure messaging features | 6–10 months | $120K – $250K | $40K – $70K |
| Enterprise | Multi-platform healthcare ecosystem with AI analytics, advanced integrations, and multi-vendor BAA management | 9–18 months | $300K – $1M+ | $80K – $250K+ |
What drives cost up
- Number of platforms (mobile-only vs web + iOS + Android)
- EHR integration depth (read-only FHIR vs bidirectional HL7)
- AI/ML features processing PHI (adds compliance review and bias auditing)
- Advanced audit logging and long-term data retention requirements
- Real-time data pipelines requiring additional encryption and audit work
- Custom infrastructure vs managed HIPAA hosting
- Geographic overlap with GDPR alongside HIPAA
What keeps cost in check
- Start with a focused MVP and expand based on real usage data
- Choose managed HIPAA hosting unless self-management is justified
- Leverage existing FHIR APIs over building custom integration layers
- Partner with a healthcare-experienced team to avoid first-time mistakes
- Reuse compliant components across features instead of rebuilding per use case
- Annual compliance cost covers audit, BAA management, security monitoring, and staff time. Many first-time healthcare teams forget to budget for it and face cash crunches in year two.
Choosing a HIPAA Compliant Software Development Partner
The development partner you choose is itself a compliance decision. A poorly chosen vendor becomes a business associate liability the moment you sign their BAA.
Use these seven criteria when evaluating companies:
- Documented HIPAA experience. Ask for case studies with specific compliance scope. Real teams describe the exact safeguards they implemented.
- BAA willingness. Vendors that push back on standard BAA language or ask to scope-reduce are a red flag.
- In-house security expertise. Penetration testing capability, SDLC maturity, named security leads.
- Healthcare domain knowledge. Familiarity with FHIR, HL7, EHR integrations, and clinical workflows.
- Cloud certifications. Documented experience with AWS, Azure, or Google Cloud HIPAA workloads.
- Transparent pricing. Compliance scope must be clearly defined in the contract.
- Post-launch support. Look for partners offering ongoing audit support and security monitoring, not just build-and-hand-off.
At Saigon Technology, our healthcare software development services team has delivered HIPAA compliant applications across telehealth features, patient engagement, and remote patient monitoring. Every engagement includes a BAA-ready process and post-launch compliance support.
Working on a HIPAA project? Talk to our healthcare team to review your architecture and compliance scope.
Common HIPAA Compliance Mistakes to Avoid
Most HIPAA breaches come from preventable mistakes, not sophisticated attacks. The Office for Civil Rights publishes enforcement summaries each year. The same failures repeat.
1. Treating HIPAA as a launch checklist
HIPAA requires ongoing risk assessments, audit log reviews, and BAA renewals. OCR settlements consistently target organizations with compliant launches but no maintenance program.
2. Missing BAAs with downstream subprocessors
Push notification services, error tracking SDKs, analytics platforms. Each is a business associate if PHI passes through. Missing BAAs remain a leading source of enforcement actions.
3. Storing PHI in non-eligible cloud services
Not every service in a cloud provider’s catalog is HIPAA-eligible. Logs routed to a non-eligible monitor, files cached in a non-eligible CDN, or backups in a non-eligible archive tier all create exposure.
4. Hardcoding access tokens and skipping least-privilege controls
Broad admin roles granted during development and never tightened before launch are exactly what OCR auditors look for. Every production role needs a documented justification.
5. Mobile-specific safeguard failures
No automatic logoff, jailbroken-device tolerance, insecure local storage, weak biometric fallback. Mobile testing must run on real devices, not just simulators.
6. Ignoring breach notification timing
The 60-day window starts from discovery, not confirmation. Build incident response protocols around fast triage and clear escalation with pre-approved communication templates.
Avoiding these mistakes starts at the architecture stage. See how our healthcare development process addresses each one.
Saigon Technology’s Experience in Secure Healthcare App Development
Saigon Technology partnered with AxiaGram to build an AI-powered telemedicine platform for US chronic care providers, running since 2021 under an ODC model.
The platform handles remote video consultations, voice-controlled note-taking, secure team messaging, and EHR integration via HL7. Built on .NET Core, Angular, and Microsoft Azure with AES-encrypted storage and HIPAA-eligible infrastructure.
Results that matter:
- 6 million+ medical records handled securely
- 40% reduction in development time
- Ongoing partnership at $70K monthly invoicing
This is what production-grade HIPAA compliant software development looks like in practice: not just encryption, but compliant infrastructure, covered vendors, and healthcare domain expertise at every layer.
Looking for more healthcare case studies and architecture examples? Download our healthcare capability deck to explore experience across telehealth, RPM, patient engagement, and healthcare SaaS platforms.
FAQs
How long does it take to develop a HIPAA compliant app?
Timelines vary by scope. MVP: 3 to 4 months. Production with EHR integration: 6 to 9 months. Enterprise healthcare platforms with AI, advanced integrations, and multi-platform support typically take 9 to 18 months. Compliance work adds 20 to 30 percent to a standard project timeline.
Can I make an existing app HIPAA compliant?
Yes, but it usually requires architecture-level changes: migrating to BAA-eligible infrastructure, retrofitting encryption, adding audit logging, and signing BAAs with all existing vendors. In many cases the retrofit cost approaches a fresh build. Evaluate early with a healthcare-experienced team.
Is AWS HIPAA compliant out of the box?
No. Compliance requires three steps from your team: sign a BAA with AWS, use only eligible services, and configure them correctly. Misconfiguration is the most common breach cause on cloud-hosted healthcare platforms. The same applies to Azure and Google Cloud.
Do I need a BAA with my push notification provider?
Yes, if notification content can include PHI. Appointment reminders, medication alerts, and lab result notifications all qualify. Many teams only catch this after a vendor audit.
What is the difference between a HIPAA-compliant app and a HIPAA-eligible service?
HIPAA-eligible services are infrastructure components (Amazon S3, Google Cloud Healthcare API, Azure Health Data Services) that can be configured compliantly. A HIPAA-compliant application is the full system built on top, covering application logic, access controls, BAAs, and the ongoing operational program. Eligible services are necessary but not sufficient.
How much does a HIPAA compliance audit cost?
External audits: $15K to $50K depending on scope. Internal annual risk assessments are required by law and typically built into the $30K to $100K annual compliance budget. Larger enterprises pursuing SOC 2 or HITRUST certifications alongside HIPAA spend significantly more.
What is the difference between HIPAA compliant app development and HIPAA compliant software development?
The terms are often used interchangeably, but there is a practical distinction.
- HIPAA compliant app development typically refers to mobile applications, patient-facing portals, and mHealth products that are built specifically for end users such as patients or healthcare providers.
- HIPAA compliant software development is a broader category that includes web platforms, backend APIs, clinical decision support systems, data pipelines, and any custom healthcare software that handles Protected Health Information (PHI), whether user-facing or not.
Both types of development require the same three safeguard layers: administrative, physical, and technical.
Conclusion
Successful HIPAA compliant app development comes down to three things.
First, all three safeguard layers must work together. Gaps in any one create audit findings.
Second, compliance is a continuous program. Build the maintenance habits and budget before you need them.
Third, partner selection is a compliance decision. Choose a team with real healthcare experience, BAA readiness, and post-launch support.
Saigon Technology supports healthcare organizations across telehealth, mHealth, RPM, and patient engagement with BAA-ready development processes and ongoing compliance support. Our healthcare-experienced teams help reduce onboarding time, accelerate time-to-market, and avoid common compliance challenges during development.
Get a free HIPAA scoping call, or download our free HIPAA compliance checklist to audit your implementation before launch.